Phishing
Pronounced as fishing, phishing, or brand spoofing is a malicious technique of tricking users into giving away personal information to an attacker. They do so by sending e-mails or creating web pages designed to collect an individual's information such as bank, credit card, or other login information. Because these e-mails and web pages look legitimate, users trust them and enter personal information. The information below shows examples of phishing attempts and ways to avoid phishing attacks and threats.
Why is it called phishing?
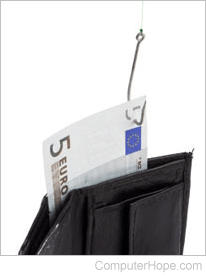
Phishing is a word play of "fishing," where someone uses a fishing pole to cast a line out into the water in hopes of catching a fish. With phishing, an attacker sends thousands of e-mails (like casting a fishing line) hoping to get someone to give them their information.
Example of a phishing e-mail
Dear eBay customer,
Your Account is Suspended. We will ask for your password only once. We will charge your account once per year. However, you will receive a confirmation request in about 24 hours after the make complete unsuspend process. You have 24 hours from the time you'll receive the e-mail to complete this eBay request.
Note: Ignoring this message can cause eBay TKO delete your account forever.
To make unsuspend process please use this link:
http://fakeaddress.com/ebay
eBay will request personal data(password;and so on) in this e-mail.
Thank you for using eBay!
http://www.ebay.com
---------------------------------------------------------------------
This eBay notice was sent to you based on your eBay account preferences. If you would like to review your notification preferences for other communications, click here. If you would like to receive this e-mail in text only, click here.
To those who frequently use online services, these e-mails may appear as if they have come from the company. However, these e-mails are designed to make a user want to click a link that helps them steal personal information such as usernames, passwords, credit card, and personal information. Below are some helpful tips on identifying these e-mails and how to handle them.
How to identify a phishing e-mail
Identifying a phishing e-mail is key to avoiding a phishing attack. Here are some things to look out for when reading e-mail.
- Wrong company - These e-mails are sent to thousands of different e-mail addresses, and the attacker has no idea who you are. If you have no affiliation with the company, it's fake. For example, if the e-mail claims to be Wells Fargo bank, but you bank at a different bank.
- Spelling and grammar - Improper spelling and grammar are often a dead giveaway. Look for obvious errors.
- No mention of account information - If the company were sending you information regarding errors to your account, they would mention your account or username in the e-mail. In the above example, the e-mail says, "eBay customer." If this were eBay, they would mention your username. However, be cautious of spear phishing, where the attacker knows some personal information.
- Deadlines - E-mail requests an immediate response or a specific deadline. For example, the above example requires logging in and changing your account information within 24 hours.
- Links - Although many phishing e-mails are better at hiding the true URL (uniform resource locator), they are still not part of the company's URL. For example, in our above eBay example, "http://fakeaddress.com/ebay" is not an eBay URL, only a URL with an "ebay" directory. If you are unfamiliar with how a URL is structured, see our URL page.
What to do if you are unsure if an e-mail is official
- Never follow any link in an e-mail. Instead of following the link in the e-mail, visit the page by manually typing the company's address. For example, in the example above, instead of visiting the fake eBay URL, type: https://www.ebay.com in your web browser and log into the official website.
- Never send any personal information through e-mail. If a company requests personal information or says your account is invalid, visit the website and log into the account as you normally would.
- Finally, if you are still concerned about your account or personal information, contact the company directly through their e-mail address or over the phone.
Issues commonly contained in phishing e-mails
Below are some issues a phishing e-mail may inquire about to trick users.
- Account issues - account or password expiring, account being hacked, account out-of-date, or account information needs to be changed.
- Credit card or other personal information - credit card expiring or being stolen, incorrect social security number or other personal information, or duplicate credit card or other personal information.
- Shipping problems - shipping company claiming a package cannot be delivered.
- Confirming orders - a request to log in to confirm recent orders or transactions.
- Someone buying or selling online - someone claiming to be interested in buying or selling something online.
Common companies affected by phishing attacks
Below is a listing of companies phishers often try to attack.
- Any major bank.
- Popular websites, such as Amazon, Facebook, Gmail, MySpace, PayPal, eBay, Microsoft, Apple, YouTube, etc.
- Government: FBI, CIA, IRS, etc.
- Shipping companies, such as DHL, FedEx, UPS (United Parcel Service), or USPS.
- Internet service providers, such as AOL (America Online), Cox, MSN (Microsoft Network), XFinity, etc.
- Casinos and lottery.
- Online dating or community websites.
I've fallen for a phishing attack, what should I do?
If you've read this page too late and have already fallen for a phishing attack, log into your account from the company's page and change your password immediately. Also, it is a good idea to scan your computer for malware, in case the site has infected your computer. Finally, if the company supports two-factor authentication, it is also a good idea to enable this feature on your account.
If you believe personal information was stolen, watch all your other accounts for suspicious activity.
Suspected phishing e-mails can also be forwarded to [email protected], an e-mail address from APWG (Anti-Phishing Working Group). APWG is a non-profit founded in 2003 and is an international coalition of counter-cybercrime responders, forensic investigators, and law enforcement agencies.
What is a phishing kit?
A phishing kit is a collection of software tools, and sometimes e-mail addresses that help a novice user target someone. These kits are developed by more experienced computer users and sold on the dark web.
419, Blagging, Catfish, Chain mail, Clickjacking, Computer crime, Computer slang, Con, Cross-site scripting, E-mail, E-mail terms, Harvesting, Hoax, Identity theft, Internet terms, Man-in-the-middle attack, Pharming, Security terms, Smishing, Social engineering, Spam, Spear phishing, Theft, Threat, Vishing, Whaling
