Secure Enclave
Secure Enclave is a hardware component of modern Apple mobile devices, like the iPhone. It is a coprocessor of the device's ARM (Advanced RISC Machine) CPU (central processing unit) in models S2, A7, and later A-series processors. It provides all cryptographic operations for authenticating the user and is designed to be secure even if the iOS kernel is hacked.
Secure Enclave was created with Apple's Touch ID technology, which can identify a user by fingerprint. They were introduced together on September 10, 2013, as part of Apple's announcement of the iPhone 5s, the first device to feature Touch ID.
How it works
- The Secure Enclave runs a dedicated microkernel and undergoes a secure boot process separate from the rest of the device. It receives its system updates independent of the other CPU components.
- During boot, the Secure Enclave generates an ephemeral encryption key and "entangles" it with a UID (user ID) inaccessible by the rest of the CPU. This key is used to encrypt and verify the authenticity of the Secure Enclave's portion of the device's memory. Any data written to NAND flash storage by the Secure Enclave is encrypted by combining this entangled ephemeral key with an anti-replay counter to prevent data tampering.
- Authentication data is sent from biometric sensors to the Secure Enclave over a serial bus. The CPU facilitates this operation but cannot read the data. The data is processed by the Secure Enclave in its encrypted memory space.
- If the Secure Enclave verifies the biometric data as authentic, it sends a message to the CPU using a "mailbox" of hardware interrupts. The CPU then permits the user to unlock or make purchases with the device.
Face ID
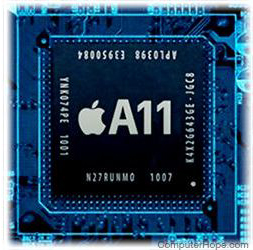
On September 12, 2017, Apple announced that Face ID, its new biometric authentication technology featured in the iPhone X, would replace Touch ID on newer devices. On the iPhone X, Face ID stores and processes all biometric data in the Secure Enclave of its ARM A11 CPU.
